|
An iterative V-Cycle Systems and software engineering is a multi-domain activity. The key however is the human factor. People from different domains speak different languages, even if they mean the same thing. This leads to misunderstanding and is one of the prime reasons why projects are late or fail. Altreonic’s “Unified Semantics” approach recognizes this from the beginning, reducing the need for continuous translations between the domains. Engineering projects can be challenging because of the complexity involved. The system can have many composing sub-systems that must fit and work together. The same applies to the engineering organization. Many skills come together and must continuously communicate and coordinate to reach the goals. To manage this challenge, decomposition and separation of concerns helps.
|
|
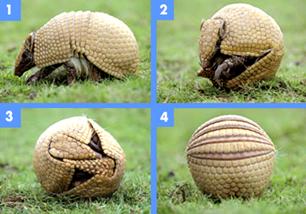
What means trustworthy? Trust in engineering is necessary because ultimately the systems and products developed are to be used by humans. Trustworthy can be decomposed in four components: Safety— This is the traditional property that is associated with high quality and reliability. However, high quality is not enough to achieve safety. Hence Altreonic decomposes use cases in three type: normal cases, test cases and fault cases. Any systems must be thought out from the beginning to satisfy all of them. If not, in the worst case human lives can be at stake. Security— While traditionally associated with the IT sector, embedded devices and systems are now everywhere. Whereas safety is dealing with |

|
Altreonic’s “Interacting Entities” paradigm is a common sense but universal approach for dealing with it. Given the complexity of systems and software engineering, a systematic approach is needed to reach a successful delivery of a system. Determining what is the right system is as important as developing it right. Reducing the complexity means reducing it up front, which is also more cost-efficient.
|
|
Keep it Simple but Smart. Nevertheless, further stages will always discover issues that were overlooked or that will provide new insights. Hence we advocate a fine-grain iterative V-model. Requirements only become final when the system is released to production. Using a modular architecture and using dependency graphs, it also becomes more cost-efficient to develop and certify a family of products. |
|
inherent risks and hazards, security deals with maliciously introduced faults. Also fellow human beings can be a risk factor. Privacy— While automating our lives, embedded systems increasingly need to register personal data that people provide because they trust the system. Again, malicious misuse of this data must be prevented and is a risk factor that must be taken into account.
|
|
Usability— The more we interact with embedded devices, the more we presume they will work and interact as we expect, certainly when we need them in a critical situation. This is a domain where human and machine become part of a larger system and hence speaking the same “semantics” is crucial for acceptance of the new technology. “”Concept” is a difficult concept”. L. Wittgenstein |